Fake Passports Being Used by Muslim Migrants
That’s what the Wall Street Journal is reporting, thanks to Jeff for sending the story.
The ‘stars’ of the WSJ piece landed in the UK, but I wonder how many are landing at an airport near you as we speak?
ISTANBUL—Somewhere over Europe, Kassem went to the airplane’s bathroom and flushed his fake Italian passport down the toilet.
When he landed in London’s Heathrow Airport a few hours later, Kassem presented his Syrian ID to U.K. immigration officials and requested asylum. The trip wouldn’t have been possible using his actual, Syrian passport—the country’s four-year civil war has turned it into a burden for anyone fleeing the conflict.
When asked where his passport was, Kassem told the officials: “It’s in the toilet.”
While hundreds of thousands of Syrian refugees make the dangerous sea voyage to Europe followed by arduous treks across the continent, some of their countrymen have used fraudulent Western passports to board planes to countries where they can request asylum. Winter’s approach, turning seas colder, stormier and more dangerous, is expected to increase the practice.
Continue reading here.
This chart shows how many successful asylum cases were processed in 2013 in the U.S. Source: Migration Policy Institute. (I would love to know what countries are represented in that 7,776 (30%) from “other countries,” wouldn’t you?)
For new readers the difference between refugees and asylum seekers is that we fly the refugees in after the UN selects them for us and asylum seekers get in on their own steam—either illegally across a border or come legally on another type of visa—then ask for asylum, claiming they will be persecuted if returned to their homeland. Once granted asylum however, the asylum seekers get all of the same welfare goodies that refugees receive.
RELATED ARTICLES:
Are refugees taking from federal programs for American poor and homeless, sure looks like it
Sacramento to welcome large number of Syrians says resettlement contractor
UNHCR Antonio Guterres leaving post at the end of the year, replacement?




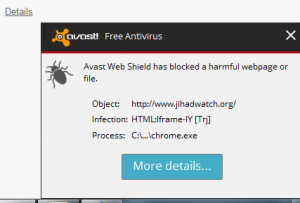
 Now about this code. I won’t post it here as text, as we know they will flag that also, but any competent developer can tell there is nothing malicious there. It’s no secret. It’s simple base64 encoding, easily decoded, not that it will mean much. The point is, it’s easy to see it’s not malicious. It’s easy for Avast to add a signature to their scanners even if they did see this scary “obfuscation.” Their choice of words is interesting: when script is “encoded” for good reason, as this is, we just call it “encoded,” not obfuscation, as developers can easily decode it to see the real code behind it, using
Now about this code. I won’t post it here as text, as we know they will flag that also, but any competent developer can tell there is nothing malicious there. It’s no secret. It’s simple base64 encoding, easily decoded, not that it will mean much. The point is, it’s easy to see it’s not malicious. It’s easy for Avast to add a signature to their scanners even if they did see this scary “obfuscation.” Their choice of words is interesting: when script is “encoded” for good reason, as this is, we just call it “encoded,” not obfuscation, as developers can easily decode it to see the real code behind it, using