Big Brother is not only watching, but gathering more power.
The modern surveillance state is referred to as an electronic police state because it uses technology to monitor people in order to detect and punish dissent. The authorities exert social control through spying, harsh law enforcement, and by regulating “privileges” such as the ability to travel. But all of this starts with surveillance.
Information is power. Imagine if agents of the State didn’t know where you live. How could it collect property taxes, arrest you, conscript you or your children, or record phone calls? Imagine if the State did not know your finances. How could it snatch your money, garnish your wages, freeze accounts, or confiscate gold? Total information is total power. That’s why the surveillance state views privacy itself as an indication of crime—not as one of violence, but as a crime against the State.
Beyond the NSA
The National Security Agency (NSA) keeps making headlines as the quintessential force behind the American surveillance state. Civil rights advocates should be equally concerned about a quieter but no less insidious manifestation: the National Counterterrorism Center (NCTC).
The NCTC coordinates at least 17 federal and local intelligence agencies through fusion centers that amass information on average Americans. A fusion center is a physical location at which data is processed and shared with government agencies. Fusion centers also receive “tip line” information from public workers, such as firefighters, who report “suspicious” behavior observed during their interaction with people. The Department of Homeland Security (DHS) and the Department of Justice (DOJ) began creating the centers in 2003. To date, there are seventy-eight acknowledged fusion centers.
The stated purpose of fusion centers is to prevent terrorist acts. But, for years, investigations have revealed that the monitoring has been used to exert social control and punish political opposition. In 2007, the American Civil Liberties Union (ACLU) published a report titled, “What’s Wrong with Fusion Centers?” One problem? Mission creep. The scope of their “protective” mission has “quickly expanded” to include the vague category of “all hazards.” The “types of information” gathered were also broadened to include non-criminal public- and private-sector data.
Two years later, the ACLU issued another paper that sketched the impact of this broadening mission. The ACLU quoted a bulletin from the North Central Texas Fusion System; law enforcement officers were told it was “imperative” to report on the behavior of their local lobbying groups, including Muslim civil rights organizations and antiwar groups.
Despite warnings, the fusion centers continue to collect data on the “suspicious activities” of non-criminals. In September 2013, the ACLU provided information from “actual Suspicious Activity Report (SAR) summaries obtained from California fusion centers.” Included in the SARs were Middle Eastern males who bought pallets of water, a professor who photographed buildings for his art class, a Middle Eastern male physician whom a neighbor called “unfriendly,” and protesters who were concerned about the use of police force.
If ever one were inclined to let such activities pass because those being watched have been Muslim, remember that power rarely restricts itself to any stated goal. As the definition of potential terrorist groups has been expanded to include groups such as the Tea Party, it has become evident that the line between terror group and political opposition has blurred.
The fusion centers share many characteristics of a surveillance state with the NSA. These characteristics include a disregard for civil rights, secret records, the use of informants, little to no transparency, the targeting of political opponents, and an ever-expanding mission.
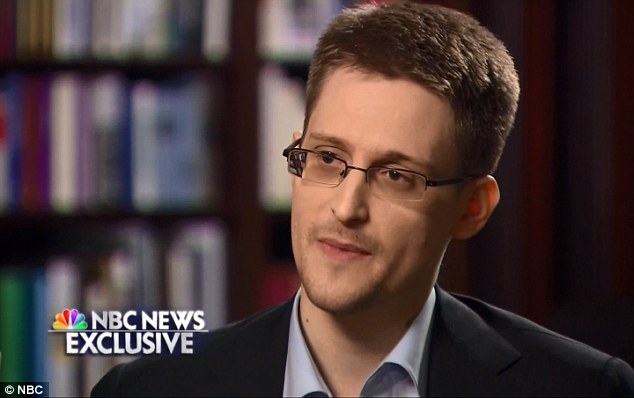
In at least one sense, the fusion centers are more typical of the surveillance state. Since Edward Snowden’s revelations, the NSA has been under a spotlight that reduces its ability to hide activities such as the warrantless recording of emails and phone calls. But fusion centers still function with little visibility. The NSA is subjected to public controversy, with civil liberty groups pushing to rein in its power. By contrast, the fusion centers are comparatively invisible, which allows them to operate covertly in a manner more typical of a surveillance state.
J. Edgar would be proud
The surveillance state was rooted in a desire to stifle political discussion, not to thwart criminal acts. In his book J. Edgar Hoover and the Anti-Interventionists, historian Douglas M. Charles traced the birth of pervasive surveillance back to the Great Debate on whether America should enter World War II. Specifically, Roosevelt wanted to support the war and to silence powerful anti-interventionists like the aviator-hero Charles Lindbergh. Thus, Hoover focused on the America First Committee (AFC) in which Lindbergh and several senators were prominent.
Hoover, director of the FBI from 1924 to his death in 1972, is the founding father of the American surveillance state. It arose because national security allegedly required constant vigilance against “the enemy,” external and internal. The internal enemy could be individuals or a concept, like communism or terrorism.
As head of the Bureau of Investigation (later the FBI), Hoover initiated the policies of extreme secrecy that bypassed the oversight of data collection. Ironically, Hoover had assumed leadership with a public pledge to end the agency’s civil liberty violations. Like surveillance agencies before and since, however, the FBI’s public statements directly contradicted its acts. For example, Hoover quietly coordinated with local police in much the same manner as the current fusion centers do. Information on a “suspect’s” sexual preferences (especially homosexuality), reports on his children and other family, as well as other sensitive data went into unofficial files that were labeled “personal, confidential”; these were inaccessible to unapproved eyes. When tidbits from the secret files were shared, the standard method was through a memo that had no letterhead, no signature, nor any other indication of the recipient or sender.
After December 7, 1941 (Pearl Harbor), America’s entry into the war became inevitable. Fearing a reduction in his power, Hoover claimed the AFC had gone underground even though the organization had clearly disbanded. Thus, Hoover continued surveillance by lying about the need to counter active subversion.
The gambit worked. Indeed, Roosevelt and subsequent Presidents were eager to weaken their opponents. The FBI’s growth was phenomenal. Charles explains, “In 1934 the FBI employed 391 agents and a support staff of 451 and was appropriated $2,589,500…. In 1945, the FBI had 4,370 agents, 7,422 support staff and an appropriation of $44,197,146.” It embraced illegal wiretapping and trespass, mail monitoring, anonymous informants, pointed investigations by government agencies such as the IRS, the selective enforcement of law, and FBI plants in targeted groups.
The Cold War built upon the information-gathering infrastructure. The Cold War’s extensive data sharing with foreign governments was also rooted in pre-WWII politics. “A hallmark of the Second World War, Cold War, and War on Terrorism, the intimate intelligence relationship between the United States and Great Britain had its origins during the Great Debate,” writes Charles.
Hoover’s secret files on political figures made him virtually untouchable. After his death, however, the FBI came under concerted attack for its domestic surveillance. The public was particularly outraged by revelations of how the FBI had targeted popular heroes such as the civil rights leader Martin Luther King. After the famous August civil rights 1963 march during which King delivered his iconic “I Have a Dream” speech, a top Hoover aide wrote in an internal memo, “In the light of King’s powerful demagogic speech … We must mark him now, if we have not done so before, as the most dangerous Negro of the future in this Nation from the standpoint of communism, the Negro, and national security.” Surveillance of King increased. Among other “information” gathered, the FBI taped an adulterous sexual encounter, which anonymously appeared in the mailbox of King’s wife.
FBI investigations into politically-oriented groups were officially restricted. Following the 9/11 terrorist attacks and passage of the PATRIOT Act, however, the FBI and other agencies gained the ability to conduct political domestic surveillance. The surveillance state that had been rooted in war and political maneuvering was given new life by the same two factors. It was also given power of which Hoover could only have dreamed.
The ACLU declared in yet another report (2008), “There appears to be an effort by the federal government to coerce states into exempting their fusion centers from state open government laws. For those living in Virginia, it’s already too late; the Virginia General Assembly passed a law … exempting the state’s fusion center from the Freedom of Information Act. According to comments by the commander of the Virginia State Police Criminal Intelligence Division and the administrative head of the center, the federal government pressured Virginia into passing the law…. There is a real danger fusion centers will become a ‘one-way mirror’ in which citizens are subject to ever-greater scrutiny by the authorities, even while the authorities are increasingly protected from scrutiny by the public.”
Since then, State surveillance has become more secretive and increasingly exempt from both oversight and accountability. Fusion centers now reach into private databases such as Accurate, Choice Point, Lexis-Nexus, Locate Plus, insurance claims, and credit reports. They access millions of government files like DMV records. Why is this important? Various laws have been adopted to prevent the maintenance of databases on average Americans, but if fusion centers access the existing files, especially private ones, they can bypass those laws.
The foregoing is a description of electronic totalitarianism. If its creation is invisible to many people, then it manifests yet another characteristic of a police state: People do not believe their freedom is gone until there is a knock on the door—one that comes in the middle of the night.
Contributing editor Wendy McElroy is an author and the editor of ifeminists.com.






 Mind control is the subject of George Orwell’s “
Mind control is the subject of George Orwell’s “